장점 1. 프로그램 작동방식을 직관적으로 배울 수 있음. 대학교에서 스택,힙,데이터,코드영역을 알려주긴 함. 근데 스택 영역이 자료구조 스택처럼 함수 호출 될 때 공간을 더 쓰고 리턴할 때 공간을 해제한다고만 배움. 드림핵에서 어셈블리, 취약점들을 배우면서 프로그램 작동방식을 직관적으로 알게 됨. 2. 컴구,운체 할 때 도움될거 같음. (글자수 부족으로 운체는 후기 X) 컴퓨터 구조를 혼자 독학해본 적이 있었음. 컴퓨터 구조 및 설계(RISC-V)이었는데 그때 배울 때는 책의 40~50퍼 정도만 이해한거 같은데 공부하고 다시 보니 파이프라이닝, 전방전달 같은 전에 추상적으로만 이해 했던게 이해 가서 재밌었음. (사실 회로 설계 공부도 해서 그렇긴 함) 단점 1. 오타 있음. 2. 설명이 가끔 생략됨.
System Hacking
시스템 해킹에서 다루는 다양한 메모리 관련 취약점의 기초 및 원리를 이해하고 단계적으로 학습합니다. 모든 과정을 마치면 시스템 해킹 상 취약점 및 공격 시나리오를 명확히 이해할 수 있으며, 바이너리를 대상으로 한 기본적인 취약점 공격 역량을 갖추게 됩니다.
System Hacking
시스템 해킹에서 다루는 다양한 메모리 관련 취약점의 기초 및 원리를 이해하고 단계적으로 학습합니다. 모든 과정을 마치면 시스템 해킹 상 취약점 및 공격 시나리오를 명확히 이해할 수 있으며, 바이너리를 대상으로 한 기본적인 취약점 공격 역량을 갖추게 됩니다.
0% 진행중
총 0개 항목 완료
강의
0 /49
제외
49
워게임
0 /26
26
퀴즈
0 /17
17
Lab은 실습 개념으로, 전체 진도율에 포함되지 않아요.
이런 이유로 이 Path를 추천해요
시스템 보안 학습은 처음엔 어렵게 느껴질 수 있지만, 기초부터 차근차근 접근하면 충분히 도전할 만한 분야입니다. 이 Path는 시스템 해킹에 관심 있는 학습자들이 스택 버퍼 오버플로 같은 기본적인 취약점부터 시작해, 단계적으로 지식과 실력을 키워나갈 수 있도록 설계되었습니다. 과정을 따라 실습하고 고민하며 스스로 문제를 해결해나가는 경험을 쌓다 보면, 어느새 시스템 보안의 핵심 개념과 원리를 자연스럽게 이해하게 될 것입니다. 이 과정을 통해 시스템 해킹에 대한 탄탄한 기초와 실전 능력을 동시에 갖출 수 있습니다. 본 Path는 기본적으로 x86-64 아키텍처 기반의 Ubuntu 22.04 및 Ubuntu 18.04 리눅스 운영체제 환경을 기준으로 합니다.
이런 내용을 배워요
- 가상 머신과 WSL을 이용한 실제 리눅스 환경 구축 및 활용법
- 컴퓨터 아키텍처 및 메모리 구조 심화 이해: x86 어셈블리, 메모리 레이아웃, 호출 규약
- 디버거(gdb) 및 익스플로잇 도구(pwntools)를 활용한 취약점 분석과 공격 방법
- 스택 버퍼 오버플로(Stack Buffer Overflow), 포맷 스트링 버그(Format String Bug), Use-After-Free (UAF), Double Free 등 주요 메모리 취약점 실습
- NX, ASLR, PIE, RELRO 등 보안 보호기법 분석 및 이를 우회하는 실전 공격 기술
- 명령 주입(Command Injection), 경로 탐색(Path Traversal), 타입 에러(Type Error) 등 논리적 취약점 분석을 통한 문제 해결 능력 강화
이런 분께 추천해요
- 시스템 해킹과 보안의 원리를 명확히 이해하고 싶은 분
- CTF(해킹 대회) 참가를 목표로 실전 기술을 익히고 싶은 분
- 화이트 해커, 보안 엔지니어, 취약점 분석가 등 보안 전문직으로 나아가고 싶은 분
이런 선수 지식이 필요해요
- 기본적인 컴퓨터 사용 능력
- 컴퓨터 구성 부품 및 컴퓨터의 동작 방식에 대한 기초적인 이해
- C/C++를 통한 프로그래밍 경험
Unit 구성
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9Stack Buffer OverflowMemory Corruption: Stack Buffer OverflowLab: Stack Buffer Overflow - Auth OverwriteLab: Stack Buffer Overflow - Memory LeakLab: Stack Buffer Overflow - Change Control Flow[함께 실습] Stack Buffer OverflowExploit Tech: Return Address OverwriteReturn Address Overwrite[함께 실습] Stack Buffer Overflow - 2Exercise: basic_exploitation_001Exercise: basic_exploitation_000basic_exploitation_000basic_exploitation_001
- 10
- 11NX & ASLRMitigation: NX & ASLRStatic Link vs. Dynamic LinkBackground: Library - Static Link vs. Dynamic LinkQuiz: Static Link vs. Dynamic Link[함께 실습] Return to LibraryExploit Tech: Return to LibraryReturn to Library[함께 실습] Return Oriented ProgrammingExploit Tech: Return Oriented Programmingrop[함께 실습] Return Oriented Programming - 2Exploit Tech: ROP x86Exploit Tech: ROP x64basic_rop_x64basic_rop_x86
- 12
- 13
- 14
- 15
- 16
- 17
- 18Double Free BugMemory Corruption: Double Free BugLab: Double Free Bug - TcacheQuiz: Double Free Bug[함께 실습] Double Free BugExploit Tech: Tcache PoisoningTcache Poisoning[함께 실습] Double Free Bug - 2Exercise: tcache_dupExercise: tcache_dup2tcache_dup2tcache_dup
- 19Format String BugMemory Corruption: Format String BugLab: Format String Bug - Memory ReadLab: Format String Bug - Memory WriteQuiz: Format String Bug[함께 실습] Format String BugExploit Tech: Format String BugFormat String Bug[함께 실습] Format String Bug - 2Exercise: basic_exploitation_002Exercise: basic_exploitation_003basic_exploitation_002basic_exploitation_003
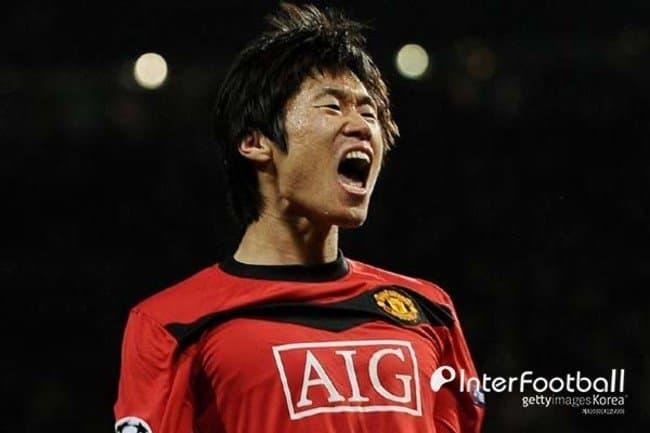
수강 후기
기초를 다지는데 도움이 됐당께
처음엔 용어부터 낯설어서 많이 막막했지만 강의를 보고 하나씩 따라 치고 직접 익스플로잇에 성공하니깐 재밌었다. 이런 강의가 많이 없는데 드림핵에서 배울수 있어 정말 좋았다. 시스템해킹의 기본적인 공격 기법들을 배울수 있어서 정말 좋았다.
모든 기법은 아니더라도, 시스템 해킹을 하기 위한 메이저한 취약점들을 대부분 다뤄서 처음 포너블 입문하기엔 매우 좋은 Path인것 같습니다
당연히 이 강의 만으로는 충분하진 않지만, 보안에 입문하고 포너블을 처음 시작할 때는 큰 도움이 되는 것 같습니다. 중간에 오타나, 설명이 부족한 부분이 있지만 알찬 강의였습니다.
0% 진행중
총 0개 항목 완료
강의
0 /49
제외
49
워게임
0 /26
26
퀴즈
0 /17
17
Lab은 실습 개념으로, 전체 진도율에 포함되지 않아요.